欢迎来到相识电子书!
标签:hack
-
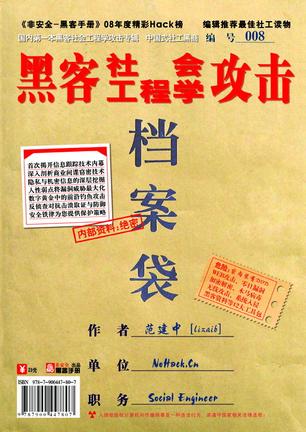
黑客社会工程学攻击
《黑客社会工程学攻击》是国内第一本涉及非传统信息安全主题的图书,非传统信息安全也泛指恐怖主义、能源、经济、文化、信息所引起的安全威胁问题。而本书将围绕个人及企业的信息威胁进行完整的部述,包括信息跟踪、隐私挖掘、商业窃密、钓鱼攻击、心理学攻击、反侦查对抗等前沿的信息安全,本书旨在帮助人们及政府、商业机构认识到社会工程学攻击的所带来的威胁,以使个人及机构重要机密免遭窃取或被入侵的危险。 国家盛会2008奥运的举办无一不说明中国进入了数字信息的时代,而新的挑战便是信息安全威胁,并且,这种发展趋势越来越严重。传统的计算机攻击者在系统入侵的环境下存在很多的局限性,而新的社会工程学攻击则将充分发挥其优势,通过利用人为的漏洞缺陷进行欺骗手段来获取系统控制权。这种攻击表面是难以察觉的,不需要与受害者目标进行面对面的交流,不会在系统留下任何可被追查的日志记录,并迫使企业内部人员转移出信息资产给社会工程学师,试图追查攻击者困难重重。 同时,每个人都不应忽视社会工程学攻击的危害性,社会工程学师表现得极为亲切,银行机构都不会怀疑使用了专业的术语而承认他们是合法的内部人员;社会工程学师也像一个魔术师,左手吸引你的注意时,右手已悄悄带走你的重要文件;社会工程学师很会说话,懂得如何操作未知的专业设备,并拥有一套信息跟踪手法,在你拨打电话给他的时候,他会开玩笑地报出你的姓名、年龄、地址、信用卡号…… 而本书的作者将向读者们展示并不为人知的社会工程学攻击内幕,由浅入深从全球头号黑客凯文米特尼克入侵五角大楼经历说起,并全面讲解社会工程学攻击 具体实施与细节,让读者们清楚地知晓他们攻击伎俩,所提供的案例可形象地认识到所带来的威胁,为免于读者们诸多的安全困扰,在第八章我提供了完整的解决方案,可使免于你受到信息伤害,企业将知道如何通过培训及相关的防护来阻碍社会工程学的攻击。 -
The Art of Deception
作者Kevin Mitnick——除此以外 还需要什么介绍? -
Binary Hacks ―ハッカー秘伝のテクニック100選
Binary Hacks from O'Reilly Japan is a book about low-level programming on GNU/Linux systems. The goal of the book is to offer useful but not necessarily very well-known techniques as many as we can to readers. Table of Contents Chapter 1. Introduction 1. Introduction to Binary Hacks 2. Terminology of Binary Hacks 3. Using "file" to tell file types 4. Using "od" to dump binary files Chapter 2. Object Files Hacks 5. Introduction to ELF 6. Static libraries and dynamic libraries 7. Using "ldd" to check dependencies of shared libraries 8. Using "readelf" to see information of ELF files 9. Using "objdump" to dump object files 10. Using "objdump" to disassemble object files 11. Using "objcopy" to embed data in executables 12. Using "nm" to see lists of symbols in object files 13. Using "strings" to extract strings from binary files 14. Using "c++filt" to demangle C++ symbols 15. Using "addr2line" to get file names and line numbers by addresses 16. Using "strip" to delete symbols from object files 17. Using "ar" to modify static libraries 18. How to link C and C++ programs 19. How to avoid symbol collision issues 20. Why PIC code is used for shared libraries on GNU/Linux systems 21. Using "statifier" to create pseudo static executables from dynamic executables Chapter 3. GNU Programming Hacks 22. Introduction to GCC extensions 23. Using inline assembler with GCC 24. Using GCC's builtin functions for optimization 25. Writing "Hello World" without using glibc 26. Using TLS (Thread Local Storage) 27. Switching glibc's internal libraries by system capabilities 28. Changing behavior of programs by linked libraries 29. Reducing exported symbols of libraries 30. Using versioned symbols to manage compatibility 31. Calling functions before main() 32. How GCC generates trampoline code at runtime 33. Allowing and disallowing executable flags of code on stacks 34. Running code on heaps 35. Creating PIE (Position Independent Executable) 36. Writing synchronized methods in C++ 37. Creating singletons in C++ 38. Understanding g++'s exceptions (throw) 39. Understanding g++'s exceptions (SjLj) 40. Understanding g++'s exceptions (DWARF2) 41. Understanding runtime cost of g++'s exceptions Chapter 4. Secure Programming Hacks 42. Introduction to GCC secure programming 43. Using "-ftrapv" to detect integer overflows 44. Using "Mudflap" to detect buffer overflows 45. Using "-D_FORTIFY_SOURCE" to detect buffer overflows 46. Using "-fstack-protector" to protect stacks 47. Why you should use unsigned constants to do bitmask 48. Why big shift operations are dangerous 49. Why you should care difference between 0 and NULL on 64-bit systems 50. Thread-safe functions defined by POSIX 51. Writing signal handlers in a safe manner 52. Using "sigwait" to process async signals synchronously 53. Using "sigsafe" to write signal processing safely 54. Using "Valgrind" to detect memory leaks 55. Using "Valgrind" to detect invalid memory access 56. Using "Helgrind" to debug multi-threaded programs 57. Using "fakeroot" to run programs with fake root privilege Chapter 5. Runtime Hacks 58. How programs reach main() 59. How system calls are called 60. Using "LD_PRELOAD" to switch shared libraries 61. Using "LD_PRELOAD" to wrap existing functions 62. Using "dlopen" to do dynamic linking 63. Showing backtraces with C programs 64. Checking running process's absolute path 65. Checking loaded shared libraries of running programs 66. Checking memory maps of running programs 67. Using "libbfd" to list symbols 68. Demangling C++ symbols at runtime 69. Using "ffcall" to call functions with dynamic signatures 70. Using "libdwarf" to get debug information 71. Using "dumper" to pretty-print struct variables 72. How to load object files yourself 73. Using "libunwind" to control call chains 74. Using "GNU lightning" to generate code in a portable manner 75. Getting addresses of stacks 76. Using "sigaltstack" to handle stack overflows 77. Hooking entering and exiting of functions 78. Modifying contexts of programs in signal handlers 79. Getting values of program counters 80. Rewriting your programs at runtime 81. Using "SIGSEGV" to validate accessibility of addresses 82. Using "strace" to trace system calls 83. Using "ltrace" to trace function calls in shared libraries 84. Using "Jockey" to record and replay programs 85. Using "prelink" to improve programs starting up time 86. Using 'livepatch" to patch running programs Chapter 6. Profilers and Debuggers Hacks 87. Using "gprof" to profile programs 88. Using "sysprof" to profile systems very easily 89. Using "oprofile" to profile systems 90. Using "GDB" to control running programs 91. Using debugging support of hardware 92. Setting break points in your C programs Chapter 7. Misc Hacks 93. How Boehm GC works 94. Why you should be careful about memory ordering of processors 95. Light-weight concurrent processing with PCL (Portable Coroutine Library) 96. Counting clock counts of CPUs 97. How floating numbers are expressed in bits 98. What's special about x86's floating numbers instructions 99. Raising signals for operations resulting infinite or NAN. 100. Further reading
热门标签
下载排行榜
- 1 梦的解析:最佳译本
- 2 李鸿章全传
- 3 淡定的智慧
- 4 心理操控术
- 5 哈佛口才课
- 6 俗世奇人
- 7 日瓦戈医生
- 8 笑死你的逻辑学
- 9 历史老师没教过的历史
- 10 1分钟和陌生人成为朋友